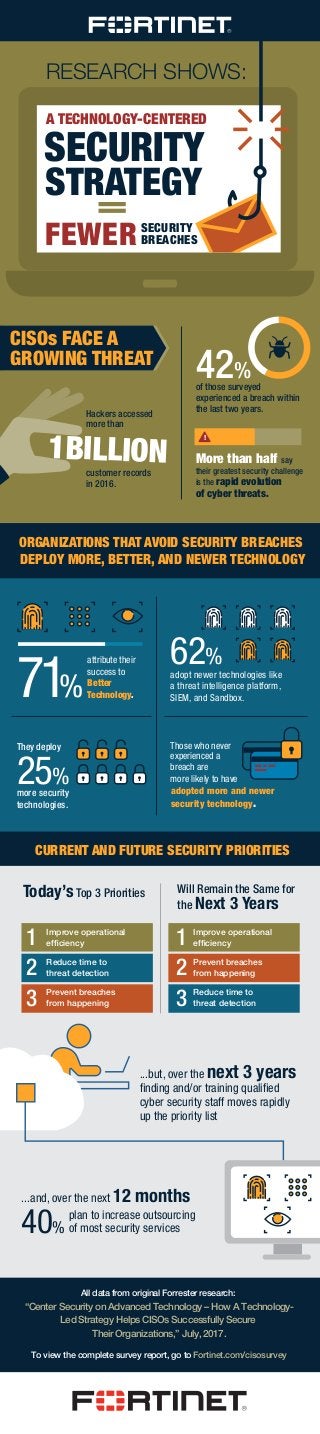
Infographic: Current and Future CISO Security Priorities
- 1. FEWER All data from original Forrester research: “Center Security on Advanced Technology – How A Technology- Led Strategy Helps CISOs Successfully Secure Their Organizations,” July, 2017. A TECHNOLOGY-CENTERED SECURITY STRATEGY = RESEARCH SHOWS: of those surveyed experienced a breach within the last two years. SECURITY BREACHES More than half say their greatest security challenge is the rapid evolution of cyber threats. adopt newer technologies like a threat intelligence platform, SIEM, and Sandbox. attribute their success to Better Technology.71% 62% Today’sTop 3 Priorities Will Remain the Same for the Next 3 Years ...and, over the next 12 months plan to increase outsourcing of most security services ...but, over the next 3 years finding and/or training qualified cyber security staff moves rapidly up the priority list 42% 1BILLION Hackers accessed more than customer records in 2016. ORGANIZATIONS THAT AVOID SECURITY BREACHES DEPLOY MORE, BETTER, AND NEWER TECHNOLOGY CURRENT AND FUTURE SECURITY PRIORITIES CISOs FACE A GROWING THREAT ! more security technologies. 25% They deploy adopted more and newer security technology. Those who never experienced a breach are more likely to have To view the complete survey report, go to Fortinet.com/cisosurvey 1 2 3 1 2 3 Improve operational efficiency Reduce time to threat detection Prevent breaches from happening Improve operational efficiency Prevent breaches from happening Reduce time to threat detection 40%
