10 Mobile Security Do's & Don'ts Infographic
•
2 likes•1,669 views
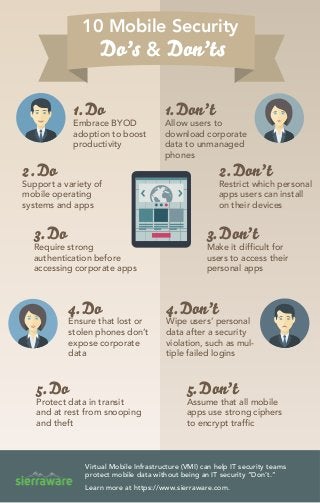
When developing a mobile security plan, learn what actions to take and what to avoid. This infographic covers the top 10 do's and don'ts to ensure a successful BYOD strategy.
Report
Share
Report
Share
Download to read offline
Recommended
More Related Content
More from Sierraware
More from Sierraware (6)
Roadmap to Healthcare HIPAA Compliance and Mobile Security for BYOD

Roadmap to Healthcare HIPAA Compliance and Mobile Security for BYOD
Cut BYOD Costs Using Virtual Mobile Infrastructure - VMI

Cut BYOD Costs Using Virtual Mobile Infrastructure - VMI
SierraVMI Virtual Mobile Infrastructure (VMI). Android-based VDI.

SierraVMI Virtual Mobile Infrastructure (VMI). Android-based VDI.
Recently uploaded
Recently uploaded (20)
Varsha Sewlal- Cyber Attacks on Critical Critical Infrastructure

Varsha Sewlal- Cyber Attacks on Critical Critical Infrastructure
A Journey Into the Emotions of Software Developers

A Journey Into the Emotions of Software Developers
The Future Roadmap for the Composable Data Stack - Wes McKinney - Data Counci...

The Future Roadmap for the Composable Data Stack - Wes McKinney - Data Counci...
Email Marketing Automation for Bonterra Impact Management (fka Social Solutio...

Email Marketing Automation for Bonterra Impact Management (fka Social Solutio...
How to Effectively Monitor SD-WAN and SASE Environments with ThousandEyes

How to Effectively Monitor SD-WAN and SASE Environments with ThousandEyes
Generative AI - Gitex v1Generative AI - Gitex v1.pptx

Generative AI - Gitex v1Generative AI - Gitex v1.pptx
QCon London: Mastering long-running processes in modern architectures

QCon London: Mastering long-running processes in modern architectures
Infrared simulation and processing on Nvidia platforms

Infrared simulation and processing on Nvidia platforms
Transcript: New from BookNet Canada for 2024: BNC SalesData and LibraryData -...

Transcript: New from BookNet Canada for 2024: BNC SalesData and LibraryData -...
Passkey Providers and Enabling Portability: FIDO Paris Seminar.pptx

Passkey Providers and Enabling Portability: FIDO Paris Seminar.pptx
React Native vs Ionic - The Best Mobile App Framework

React Native vs Ionic - The Best Mobile App Framework
Zeshan Sattar- Assessing the skill requirements and industry expectations for...

Zeshan Sattar- Assessing the skill requirements and industry expectations for...
Emixa Mendix Meetup 11 April 2024 about Mendix Native development

Emixa Mendix Meetup 11 April 2024 about Mendix Native development
Use of FIDO in the Payments and Identity Landscape: FIDO Paris Seminar.pptx

Use of FIDO in the Payments and Identity Landscape: FIDO Paris Seminar.pptx
All These Sophisticated Attacks, Can We Really Detect Them - PDF

All These Sophisticated Attacks, Can We Really Detect Them - PDF
[Webinar] SpiraTest - Setting New Standards in Quality Assurance![[Webinar] SpiraTest - Setting New Standards in Quality Assurance](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar] SpiraTest - Setting New Standards in Quality Assurance](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[Webinar] SpiraTest - Setting New Standards in Quality Assurance
Microservices, Docker deploy and Microservices source code in C#

Microservices, Docker deploy and Microservices source code in C#
10 Mobile Security Do's & Don'ts Infographic
- 1. 10 Mobile Security Do’s & Don’ts 1.Do Embrace BYOD adoption to boost productivity 1.Don’t Allow users to download corporate data to unmanaged phones 2.Don’t Restrict which personal apps users can install on their devices 2.Do Support a variety of mobile operating systems and apps 3.Don’t Make it difficult for users to access their personal apps 3.Do Require strong authentication before accessing corporate apps 4.Don’t Wipe users’ personal data after a security violation, such as mul- tiple failed logins 4.Do Ensure that lost or stolen phones don’t expose corporate data 5.Do Protect data in transit and at rest from snooping and theft 5.Don’t Assume that all mobile apps use strong ciphers to encrypt traffic Virtual Mobile Infrastructure (VMI) can help IT security teams protect mobile data without being an IT security “Don’t.” Learn more at https://www.sierraware.com.
